Encryption is one of the most amazing technologies to secure data. It prevents any 3rd-party from accessing it without having the key that unlocks the encrypted data, and hence everybody can secure their files simply via encrypting it with good methods.
Encryption is used everywhere; in HTTPS protocol to transfer secure data between your browser and web servers, and in banking applications to prevent 3rd-parties from messing with your banking information… Any program that processes or protects important data will definitely be using encryption.
But what most people don’t realize is that encryption also provides protection against data restoration, especially on SSDs.
Table of Contents:
What’s The Relationship Between Encryption & Data Restoration?
What most people don’t realize is that a quick format or disk deletion does not actually delete their data, and a large portion of it is still recoverable later. In one way, this can be helpful to recover your data if you have not taken a backup using a reliable software like Remo Data Recovery tool. But what if the important data falls in the wrong hands? This is sad because the average Tom simply runs a format before selling his old devices without knowing that the format doesn’t actually delete his files for the new owner, and that the latter can still recover it.
You see, when you delete your files on SSDs (Including SD Cards), they are not actually deleted instantly, and rather, what happens is that the current filesystem will simply detach the file node from its data to prevent accessing to it, aka “deleted”. But the file data is still there in fact and isn’t fully deleted until new data comes and overwrites it at a random later time and probability [1].
And this is a problem because SSDs are designed in a way such that it is practically impossible to overwrite specific places on them, because since too much I/O hurts SSDs on the long run, they were designed to spread data writing operations across the disk rather than focus on specific sectors of them. Had this not been the case – just like with HDDs – then any data wiping programs like shred, wipe and srm would have been enough to delete the data forever, but sadly it isn’t.
So to sum up, your deleted files are never in fact deleted on an SSD, unless the OS overwrites it somehow in a later time with new data coming in, but you can never know for sure.
Which is why encryption becomes more important; Not just to protect your files from 3rd-party access and not just to prevent a thief from accessing it even if your laptop was stolen… But also to make sure that the deleted files can never be restored by a 3rd-party.
Linux Encryption Support

Almost all Linux distributions do support disk encryption by default at the time of installation, such as Ubuntu, Fedora, Mint, openSUSE… Almost all of them. All you have to do during installation is to toggle one checkbox (In the image above for example), and that’s it.
If you are already using a non-encrypted installation, then the process of transforming into a fully encrypted one can be hard, depending on the Linux distribution you use. And you may never succeed in doing it; So a better approach would be to backup your data and then run a full new installation with encryption enabled.
After you install the new OS, you may restore your data to your new partitions.
Notice however that there are various ways and methods of doing encryption, and while the default Ubuntu encryption – for example – will encrypt both your home and root partitions (If you separated them), it will not encrypt the second stage bootloading files, leaving your PC vulnerable to RAM & kernel attacks at boot times.
Hence, Full Disk Encryption should be used if you are so much worried about your data, but most folks out there would be just fine with the normal encryption options.
How to Encrypt Files & Folders on Linux
If you still prefer to use your non-encrypted installation, then what can not fully achieved shouldn’t be completely left; You can at least encrypt your most sensitive data & files without having to encrypt the full disk.
To do that, there are special programs which enable you to create secure “vaults” to put your files inside them. These vaults are encrypted with strong encryption methods and protected by a password, so that only you can access it.
We recommend using VeraCrypt on Linux do the job. You can download it from its official website and install it according to the Linux distribution you use.
1- Its workflow is quite simple; Just create a vault with the options you would like:

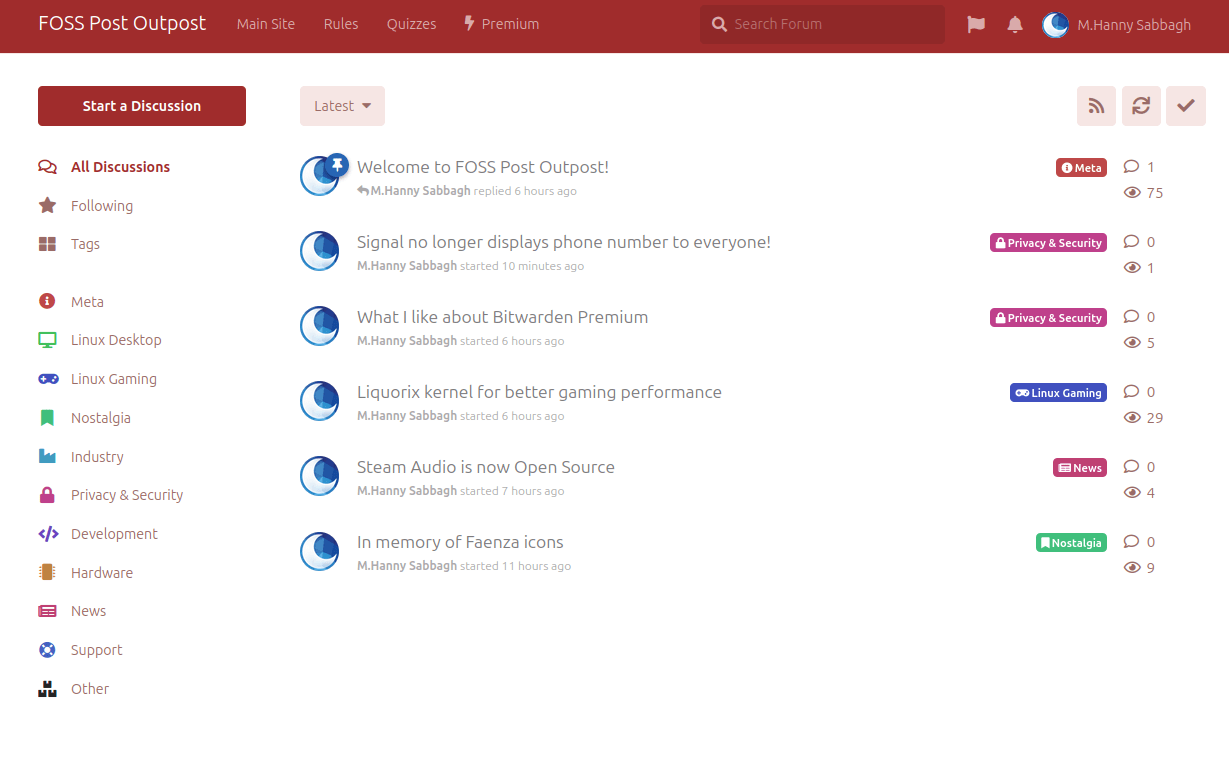
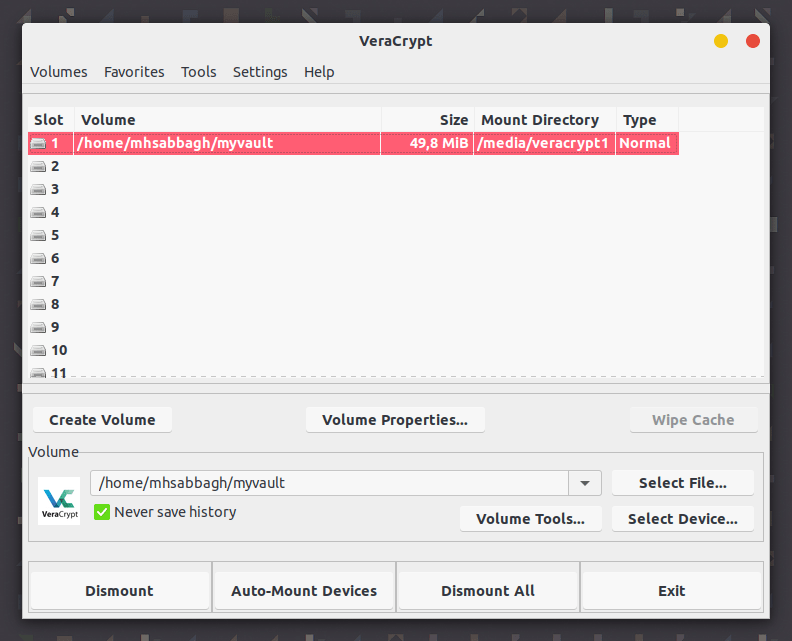
2- Then mount it (After clicking on the “Select File” and choosing the vault you created):
3- And you’ll be able to put your files inside it to secure them:
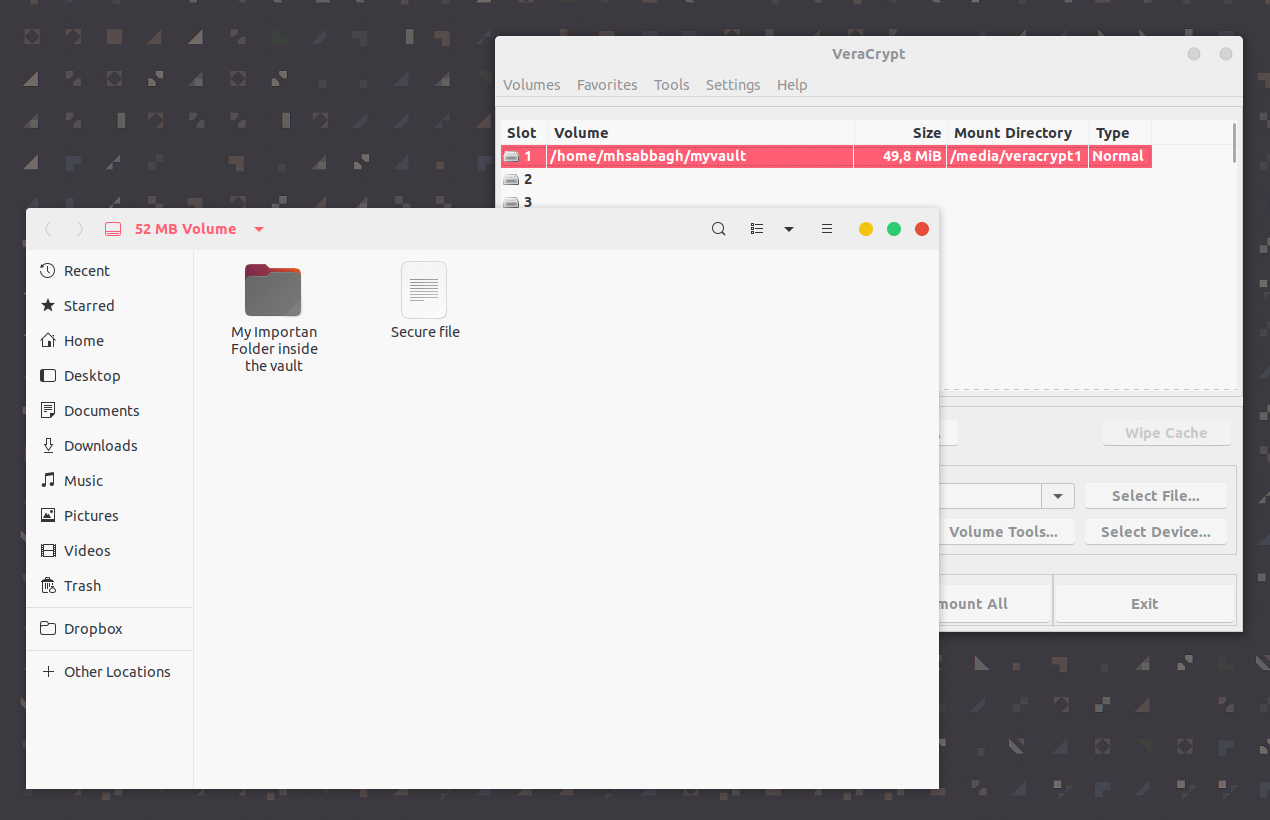
That’s it.
Conclusion
Encryption is a very important extra layer of protection that everybody should having. It protects your files from being accessed by a 3rd-party in many situations such as theft or selling your old devices, and all it takes is few extra steps to enable.
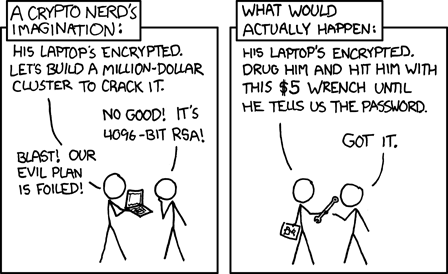
Of course, it may not protect you under full dictatorship governments, for example. Relevant Xkcd:
Sadly, for the average cases, most people don’t know about encryption and how important it is to use. Hence, they lose this extra layer of protection and risk their data being exposed.
A good Linux user with a sense of security should definitely be using encryption for almost all of his/her devices.
To get encryption on a Linux server, you should get an SSL certificate, which can be of a different type. To choose the right SSL, you can ask the SSL provider. Even all Linux distribution platforms support encryption. HTTPS when enabled, it saves files and folders from being accessed by a third party
FOSS Post is a high-quality online magazine about Linux and open source software. With a team of professional writers from all over the world, we bring you the latest articles, analysis and reviews related to open source.
Articles published with this account are written as a collaborative effort between writers. You can email us at contact@fosspost.org